Why IoT Devices Should Never Have a Public IP Address
Recent years have seen global industries embrace IoT devices to solve any number of potential operational and business challenges. Every walk of life, from manufacturing to healthcare, construction to education, now looks to connected smart devices to help address the needs of an ever-evolving world. It’s no wonder, then, that Fortune Business Insights predicts the global IoT market could reach $1.85 trillion by 2028.
Unfortunately, with this increased profile comes increased risk from bad actors targeting these connected devices for their own nefarious purposes. One report from cybersecurity services provider Kaspersky identified around 1.5 billion attacks on IoT devices (primarily using the Telnet protocol) in the first six months of 2021 alone.
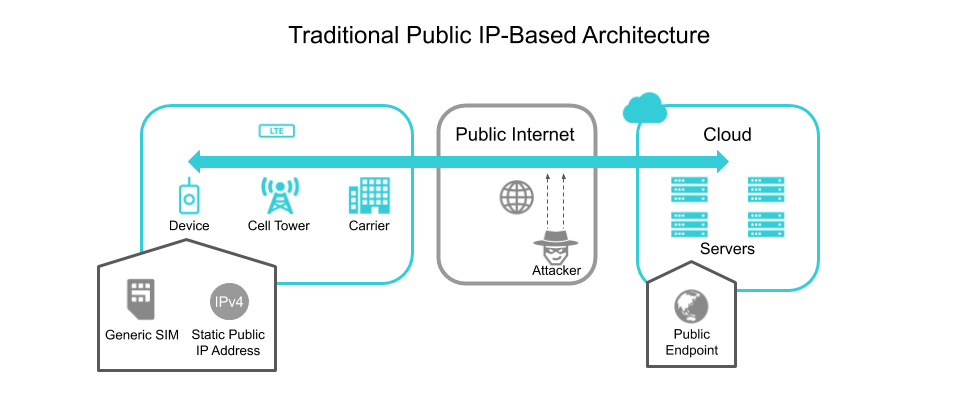
Internet Protocols (IP) are common targets for hackers looking to illegally access devices and the networks in which they operate. Public IP addresses, in particular, pose a considerable risk for IoT deployments that manage large fleets of devices. Let’s examine why.
What Are The Risks Associated with Public IP Addresses?
At the most basic level, an IP address essentially identifies a user when they connect to the internet. Public IPs are assigned to users by their ISP and cover entire networks, meaning that every device within said network uses the same identifier when connecting to the internet. This means that every individual IoT device in a deployment can be tracked and monitored remotely.
This also means that every single device creates a potential entry point for bad actors. By exploiting various vulnerabilities, hackers can access your network and steal data, introduce DDOS attacks, or even infect your system with ransomware. There are even publicly available search engines that can allow these nefarious presences to scan public IP addresses for these vulnerabilities, potentially illuminating hundreds or even thousands of bugs within a fleet.
All this is to say that a static public IP address introduces a considerable security risk for any deployment that must be architected around.

Private Vs Public IP Addresses
The limitations in the number of IPv4 addresses possible using the protocol’s 32-bit taxonomy inspired the creation of private IP addresses. Private IP addresses are used to securely connect a group of devices within a private network, yet for external connections to the internet, however, a public IP address must still be employed – in a manner of speaking.
Essentially a number of IP address ranges have been dedicated for use within private networks, utilizing Network Address Translation (NAT) to translate data from its source into a global IP address before it is sent to an external network. This allows for multiple devices to connect to the internet using a single public IP address.
This architecture allows IP addresses within the private IP range to be reused from network to network, making it easier to group scores of devices without each one requiring access to the public internet. Furthermore, the use of NAT creates a “stateless firewall,” which blocks unauthorized connections from reaching the private network. This does mean these are unable to be accessed from an external network without some means of working around the NAT.

What About IPV6 Deployments?
Though it is often touted as the successor protocol due to many of its unique design elements, IPV6 is engineered in such a way that the risks posed by connections to the public internet may be of even greater concern for IoT architects.
IPV6 does away with the 32-bit taxonomy of its predecessor in favor of a 128-bit address that yields 340 Undecillion unique alphanumeric combinations. The nearly endless supply of addresses available under IPV6 makes it feasible that every individual device connecting to the internet could have its own unique IP.
Of course, having an individual public IP address exposes these devices to the same inherent risks of unsecured IPv4 addresses, so which protocol is selected is irrelevant if the proper precautions are not taken.

How Should I Secure My Deployment?
The surest way to secure your system from potential incursions brought on by public IP addresses is to not use a public IP at all. For those deployments where this is not an option, however, there are several solutions out there that range from simple best practices to avoid common mistakes to powerful tools that safeguard your data from all but the most tenacious hackers.
For common-sense solutions, let’s start by changing the default passwords on all devices (including sensors, routers, and gateways) and keeping your systems current with firmware updates and security patches. This won’t entirely eliminate the threat of incursions, but it will make your data more difficult for the average hacker to obtain, as most breaches stem from unsecured devices.
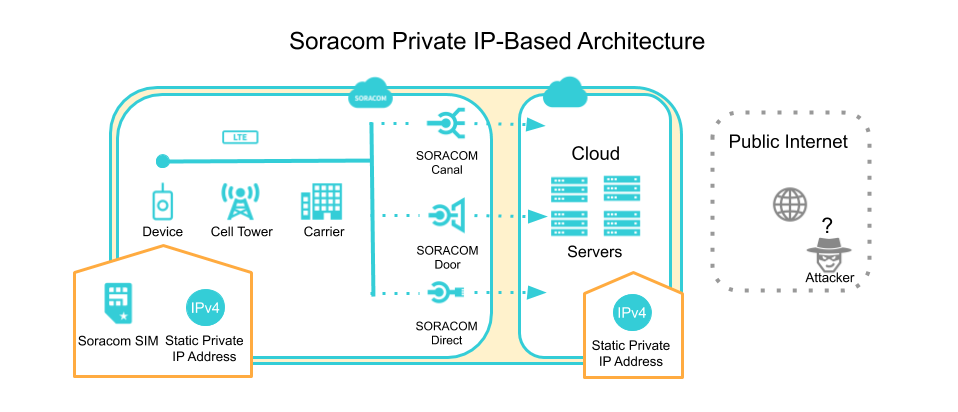
For more earnest security efforts, Soracom users can deploy the Virtual Private Gateway (VPG), which segregates their cellular traffic from that of other networks. The service allows users to control each of their devices’ IP addresses, filter or block access to the public internet, and manage device-to-device communications at the granular level.
The VPG pairs naturally with Soracom Canal, which creates a virtual private cloud (VPC) peering connection between your deployment and an AWS VPC. Should your backend services lie in another cloud service, Soracom Door can be used to create an IPSec site-to-site VPN between your VPG and cloud service of choice. If you’re eschewing the cloud in favor of a data center, then Soracom Direct provides a dedicated fiber channel via AWS Direct Connect.
Outside of private networking solutions, Soracom offers services like Funnel and Funk that help secure the connection between your devices and the cloud service of your choice, as well as Napter which provides on-demand remote access to your network’s devices while employing a number of features that limit the risks associated with public IP addresses.
………………
Got a question for Soracom? Whether you’re an existing customer, interested in learning more about our product and services, or want to learn about our Partner program – we’d love to hear from you!
MORE LIKE THIS




What is Soracom?
Discover why technology innovators choose Soracom for connecting their
devices to the cloud over cellular.

Soracom's Picks
Advices and interviews, to inform and inspire.

Why Bluetooth + Cellular is the Secret Sauce for Modern RTLS
How Cellular and Bluetooth is Powering RTLS Growth The world…

Moving Toward Seamless IoT: How SGP.32 Addresses Critical Connectivity Gaps
Why SGP.32 Changes Everything for IoT For years, the promise…

[Podcast] No More Dark Spots: Mastering RTLS and Asset Tracking with Lamplight Logistics
Building in IoT is never a straight line. Welcome back…

Cloud Native
IoT Connectivity Platform
Soracom built the worlds first cloud-native connectivity management platform, built on AWS. Learn more about going beyond connectivity.






