Are Known Vulnerabilities the Biggest Threat to IoT Security?
As the IoT continues to grow and expand, so do the risks associated with our smart devices. A 2019 survey from Statista found that roughly ⅓ of all companies deploying IoT solutions worried that attacks on their connected devices could negatively impact their operations – and more recent statistics are lending credence to those concerns.
An astonishing 1.5 billion breaches traced back to IoT devices are estimated to have occurred in just the first six months of 2021, according to cybersecurity firm Kaspersky. This is roughly double the incursions observed in the previous year, with most of the attacks utilizing vulnerabilities within IoT architecture or the devices themselves to access sensitive data.
IoT devices are not typically created with security in mind, and the fact that they lack the processing power to detect or respond to intrusions means there can often be gaps in code or bugs that can be exploited by bad actors if not properly addressed. Though some can be patched out, new vulnerabilities are almost constantly being discovered.

Even IoT Platforms Are Not 100% Safe
One such vulnerability is called “Access:7,” a set of remote code execution (RCE) flaws recently uncovered by Verdere Labs and CyberMDX. The issues stem from existing flaws within the IoT device management platform Axeda, and – if properly exploited – could allow hackers to take full control of a host operating system. This would give them full access to sensitive user data, and allow them to remotely execute code, change file configurations or issue denial-of-service commands.
Of the 150 IoT devices known to be at risk from the Access:7 vulnerabilities, the majority are medical in nature – a fact that has inspired many within the industry to issue alerts to hospital systems and healthcare providers that could be vulnerable to attack.
This comes at a time when malware attacks on medical IoT devices are on the rise. Because medical devices require approval from governing bodies like the FDA, it can sometimes take years for a product to get approved and into hospitals. This means that many items are being shipped with outdated technology and known vulnerabilities.
Most troubling among this collection of vulnerabilities is three RCE flaws that have been labeled critical threats through the common vulnerability scoring system. Two have received a CVSS score of 9.8 and relate to the hardcoded credentials that allow for full remote control of a device, as well as a flaw in a remote server command that can grant full file-system access and enable remote code execution.
The remainder of the flaws range in severity from 5.3 to 7.5 on the CVSS scale, and could also be exploited for DoS attacks or to access user data.

OpenSSL Vulnerabilities May Invite Hackers Into Smart Homes
A 2020 survey found that the average American household contained more than 10 connected devices. Yet gadgets using outdated encryption tools may be allowing uninvited guests into these homes.
A group of researchers recently monitored the usage of over 50,000 smart home devices through a proprietary program called IoT inspector. Though they were looking to observe how these devices behaved over their local networks, what they found was that many of these items are utilizing out-of-date versions of OpenSSL to encrypt their traffic.
Though they were unable to pinpoint the precise versions of OpenSSL being used in these devices, researchers did note that the manufacturers had ample time to address these issues during development.
OpenSSL is frequently updated to address bugs, vulnerabilities, and exploits that have been discovered, so using outdated or unpatched versions of these software libraries opens networks up to all kinds of risks. Out-of-date software in a smart home device could allow bad actors to access user data, access camera or audio receptors, or alter a device’s programming.
Addressing Vulnerabilities With Hardware
One of the most commonly exploited vulnerabilities in connected IoT devices is via side-channel attacks (SCA), which use information gained from the actual performance of a device rather than flaws in coding or encryption. Some phenomena that these attacks target include current, execution time, and electromagnetic emissions. SCAs are particularly effective when targeting the keys to algorithmically operated cryptographic operations.
“If some data is being processed and there is a secret key used to encrypt or decrypt it, SCAs could be used in some cases to recover this key,” MIT grad student Saurav Maji, told The Indian Express. “It can be applied to any data that you want to keep secret.”
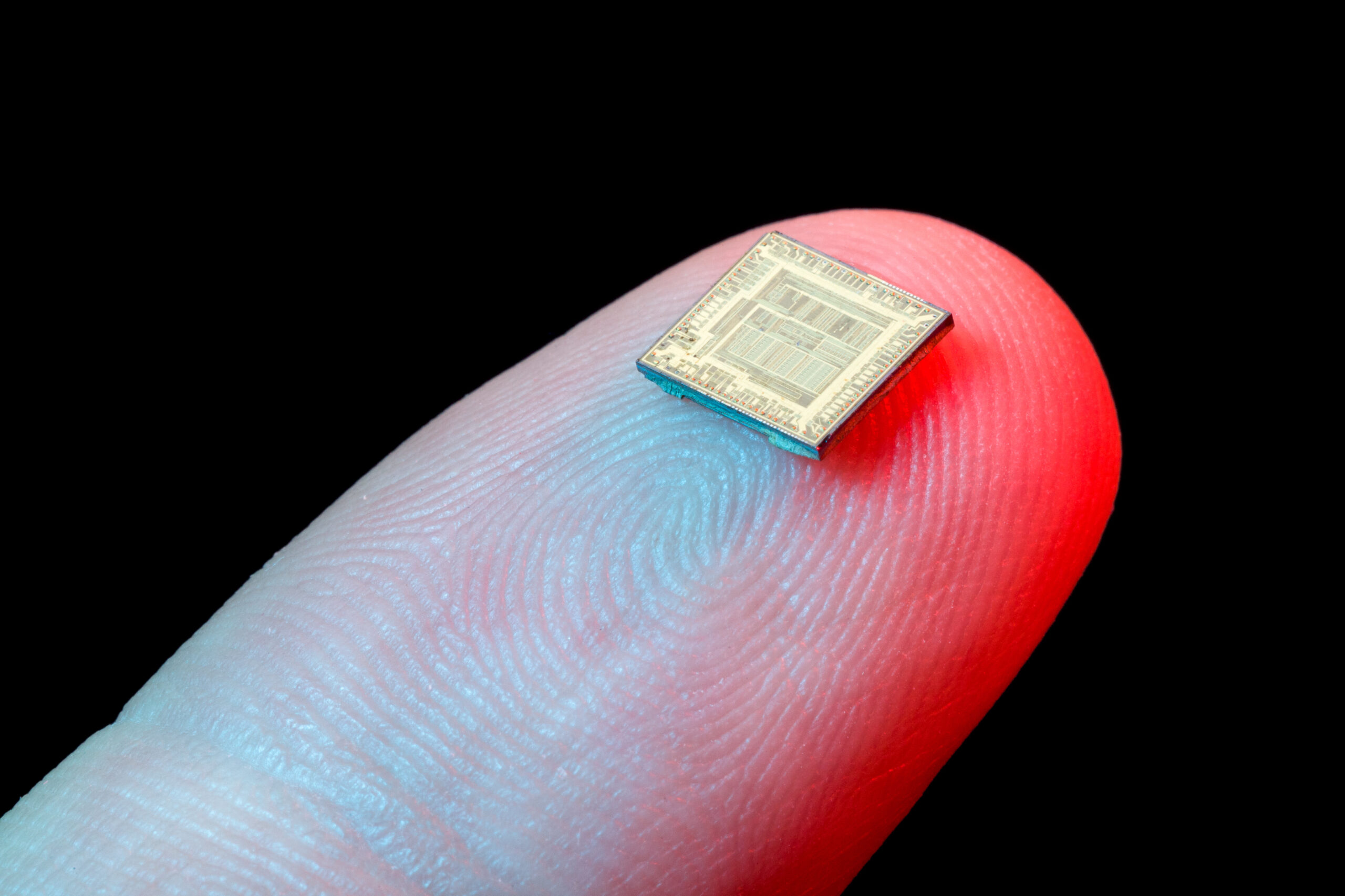
In an effort to better defend IoT devices from these kinds of attacks, Maji and a team of engineers have created a low-power integrated circuit chip no bigger than a thumbnail that utilizes a unique computational process to throw off would-be attackers.
Dubbed threshold computing, the process eschews more traditional neural networks and instead splits data into segments at random, processing them in an equally random order before assembling them into actionable intel. This ensures that any data leaked is random, and all but unusable for SCA attackers.
Though the process does ask a bit more of a device’s computational abilities, as well as its memory, researchers have simplified the computational math to reduce power consumption. For his part, Maji believes this tradeoff may be worth it for the security it provides.
“By using this special function, we can perform this operation while skipping some steps with lesser impacts, which allows us to reduce the overhead,” said Maji. “We can reduce the cost, but it comes with other costs in terms of neural network accuracy. So, we have to make a judicious choice of the algorithm and architectures that we choose.”

The Best Defence May Be Common Sense
When securing your IoT deployment, there are many things you can do, but the simplest and most effective way to protect your data may simply be to stay current. Be sure that your devices are using the most up-to-date software, and be mindful of any patches. Avoid using default passwords, and ensure that your data is safely and securely transmitted.
For those developers looking for added security, Soracom offers a number of solutions that could help maintain the integrity of your data. At the most basic level, the Soracom IoT SIM card provides carrier-grade encryption to help defend your data – and that’s before you look at our additional services.
From private networking tools like Soracom Door and Soracom Canal, to private device-to-device LAN connections via Soracom Gate, to the secure provisioning provided via Soracom Krypton, Soracom has a solution to help keep your IoT devices secure and protected from incursion attempts.
………….
Do you have questions about an IoT project? Speak with one of our experts today to learn how Soracom has helped more than 20,000 innovators deploy, scale, and secure their IoT projects.
MORE LIKE THIS




What is Soracom?
Discover why technology innovators choose Soracom for connecting their
devices to the cloud over cellular.

Soracom's Picks
Advices and interviews, to inform and inspire.

Why Bluetooth + Cellular is the Secret Sauce for Modern RTLS
How Cellular and Bluetooth is Powering RTLS Growth The world…

Moving Toward Seamless IoT: How SGP.32 Addresses Critical Connectivity Gaps
Why SGP.32 Changes Everything for IoT For years, the promise…

[Podcast] No More Dark Spots: Mastering RTLS and Asset Tracking with Lamplight Logistics
Building in IoT is never a straight line. Welcome back…

Cloud Native
IoT Connectivity Platform
Soracom built the worlds first cloud-native connectivity management platform, built on AWS. Learn more about going beyond connectivity.






