Unsecured Devices Highlight the Need for Advanced IoT Security

IoT Security should be one of the first things that developers consider when plotting out a deployment. Even with a reported $145 billion spent worldwide on overall cybersecurity in 2020, cybercrimes in the same period cost the global economy roughly $945 billion. The challenge is serious, and the growing number of weakly-defended IoT devices have come to represent an attractive target for both malicious hackers and organized criminal enterprises.
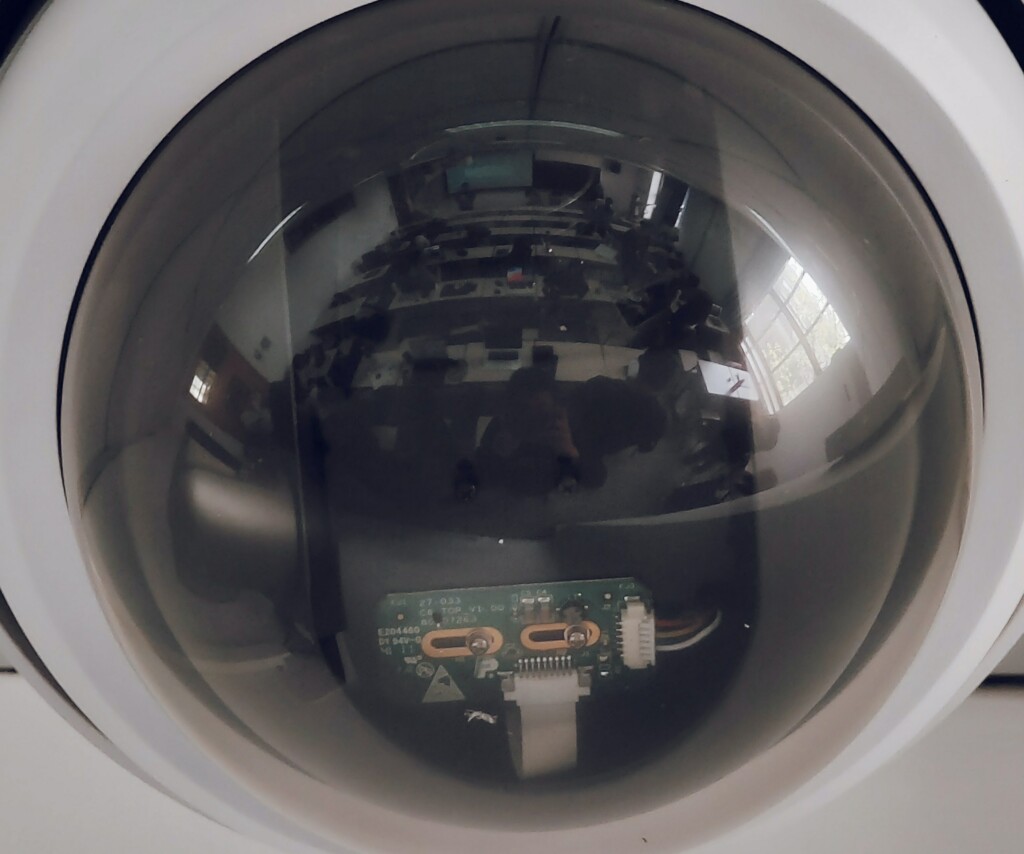
As the technology surrounding IoT continues to evolve, hackers and cybercriminals have employed increasingly sophisticated methods to access sensitive data. Whether it be exploiting a faulty random number generator to access encryption keys, or logic and flow vulnerabilities allowing hackers to capture live video and access credentials, today’s cybercriminals are increasingly clever in their approach.
As such, it’s important to recognize potential entry points for data incursions on IoT devices.
It Starts with Unsecured IoT Devices
For IoT developers, the main threat vector comes from unsecured devices. Due to their limited power and computing capabilities, most IoT devices are designed without built-in security features. This leaves them highly vulnerable to hackers, who can wreak all kinds of havoc should they gain access to your systems.
Unsecured IoT devices can expose networks through weak authentication protocols, legacy password hashes, hidden backdoors, and buffer overflows stemming from insecure string-handling functions.
Open source components from third parties also present a considerable risk of incursion, as the firmware is often released with known vulnerabilities intended to be patched in later updates. Even debugging logs, which are often left in production devices, can be scanned for weak points to grant access.
“[The] issue involves device manufacturers, who are often in charge of performing device security despite commonly lacking the appropriate security controls to scan for firmware layer vulnerabilities,” Baksheesh Singh Ghuman of Finite State told TechNews World.
“As a result of these factors, firmware vulnerabilities are often ignored and become cybersecurity blind spots which draw the attention of threat actors.”
The Cost of Complacency with IoT Security
Between downtime, troubleshooting, and any ransomware, the financial impact of a cyber attack can be considerable. In 2017, a survey from Altman Vilandrie & Company found that IoT security breaches could cost small-to-medium sized businesses up to 13% of their annual revenue. Larger companies may be better equipped to weather the storm, though the cost for firms with average revenue above $2 billion was still $20 million.
“IoT attacks expose companies to the loss of data and services and can render connected devices dangerous to customers, employees and the public at large. The potential vulnerabilities for firms of all sizes will continue to grow as more devices become Internet dependent.”
Stefan Bewley, director of Altman Vilandrie &Company
Elsewhere, a 2019 study performed by Irdeto estimated that cyber attacks targeted specifically at IoT devices could cost the US economy as much as $8.8 billion annually. Of the 200 security decision makers surveyed, roughly 80% had experienced an incursion in the past twelve months, with more than half of those attacks resulting in considerable downtime for their organization.
With the number of connected devices growing exponentially, IoT security should be a top priority for anyone launching or scaling a project.

An Investment in the Future of IoT Security
Fortunately, it looks like the increased investment in IoT isn’t limited to devices and platforms. A new study by Juniper Research suggests that spending on IoT security could reach as high as $6 billion by 2023 – an increase of 300%.Elsewhere, research firm Technavio is claiming that the IoT security market is set to grow by $83.25 billion between 2021 and 2025 with a CAGR of over 30%.
Fortunately, the Soracom IoT platform comes with a number of security features that help ensure the stability of your deployment. Whether you’re looking to establish a private network via Soracom Canal or Soracom Door, enable network monitoring with Soracom Junction, or securely provision IoT certificates to devices via Soracom Krypton, Soracom offers a wealth of options to better secure your IoT devices.
If you are looking for a secure IoT connectivity provider, or have questions about Soracom’s blended network of IoT solutions, you can speak with us today!