What you’d build without Soracom Beam
|
Add full TLS stacks to device firmware
Embed and rotate cloud credentials on every device
Operate your own proxy or relay server |
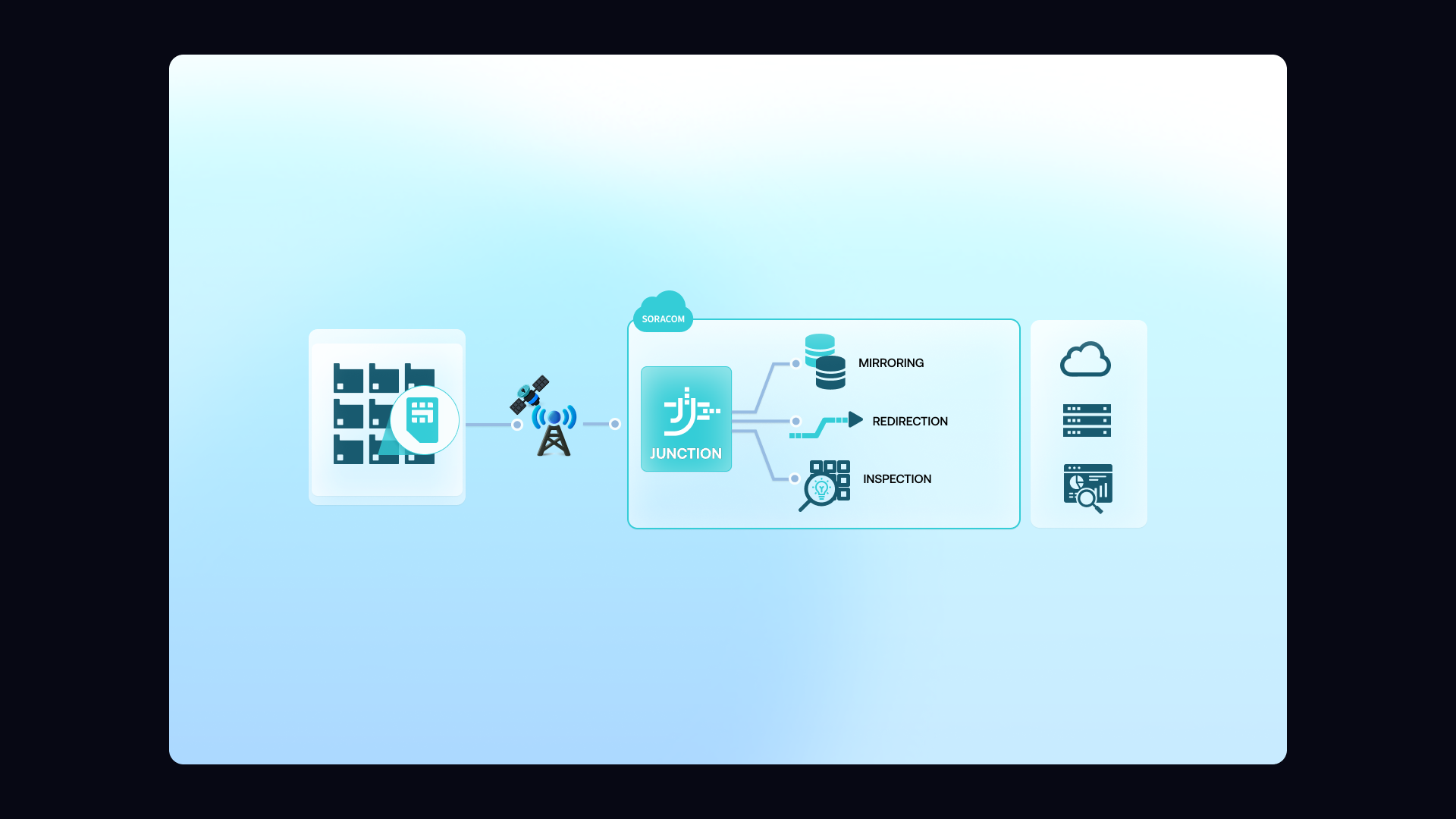
Soracom Junction
Packet-level mirroring, filtering, and routing service
Gain deep visibility into device traffic and route it where you need it
Monitor, inspect, or redirect device traffic with full control inside your private network
Junction lets you mirror packets to a monitoring system, apply custom routing rules, or filter traffic based on ports and protocols. This is invaluable for debugging device behavior, capturing anomalies, analyzing security events, or integrating advanced tooling like NDR systems. Because Junction operates inside the Soracom VPG, traffic never touches the public internet—giving you safe, private access to raw network data.

Why use Soracom Junction for your project?
Deep network insight
Observe real device traffic in real time without touching device firmware.
Control behavior
Filter or block unwanted traffic before it reaches backend systems.
Route intelligently
Forward packets where they’re needed for analysis, logging, or automation.
How it works
Packet mirroring for real-time visibility
Junction duplicates device traffic and forwards it to a monitoring tool, NDR system, or analysis engine. This lets you observe device behavior, detect anomalies, and troubleshoot issues without modifying firmware.
Filter and control traffic at the network edge
Apply rules to allow, block, or redirect traffic based on source, destination, port, or protocol. This adds security and ensures only approved traffic reaches your backend applications.
Route packets to private monitoring systems
Send mirrored traffic to your VPC or private network using Soracom Canal, Door, or Direct. This creates a secure, private pipeline for packet inspection, analytics, or compliance logging.
Architecture and implementation
Soracom Beam sits between devices and cloud endpoints, acting as a lightweight protocol proxy. Devices send basic HTTP, TCP, UDP, or MQTT traffic to a Soracom endpoint. Beam then adds encryption, injects API keys or certificates, optionally performs protocol conversion, and forwards the data to your chosen cloud destination. It’s ideal for reducing device-side complexity, improving battery life, and enabling secure data ingestion without managing edge-side credentials.
Enable Soracom Junction and choose the inspection or mirroring mode
Open the Soracom User Console and navigate to the SIM group where you want to inspect or route traffic.
Enable Soracom Junction in the group settings, then select the mode you need: Mirroring for copying packets to another destination, or Inline Processing for forwarding traffic through an inspection or filtering system.
Junction lets you observe or manipulate traffic without modifying device firmware or deploying additional hardware.
Setup steps are outlined in the Soracom Junction documentation.
Configure the target endpoint for traffic mirroring or inline forwarding
Specify the destination where mirrored or forwarded traffic should be sent—such as a packet capture server, SIEM platform, intrusion detection system, or your own analytics endpoint.
For mirroring, Junction copies packets without affecting device behavior. For inline processing, Junction forwards packets through your inspection system before routing them to the intended destination.
This configuration allows deep visibility or policy enforcement without changes to your network or device architecture.
See configuration details in the Junction configuration guide.
Monitor, analyze, or filter traffic using your connected systems
Once Junction is active, monitor mirrored or processed traffic from the destination system you configured.
Use your preferred tools—such as packet analyzers, SIEMs, intrusion detection systems, or custom filters—to review device traffic for debugging, security inspection, or compliance monitoring.
Junction enables ongoing visibility without disrupting normal device operation or requiring firmware updates.
Learn more in the Monitoring traffic with Junction documentation.
How Soracom Beam works with other Soracom services
|
Use Beam + Funnel for built-in cloud adapters
Use Beam + Canal or Door for private networking
Use Beam + Harvest/Lagoon for diagnostics |
