SORACOM Gate ensures direct communication with IoT devices via VPG

Soracom Gate VPG Safely Connects IoT Devices

Introduction
Since launching our IoT platform on 30 September 2015, many of our customers have used SORACOM Air IoT SIM cards to connect a number of devices over 3G/LTE, giving rise to a number of IoT ecosystems. After the launch, I met many customers at various events & received consistent requests to enable “direct communication with devices.” Today we are announcing SORACOM Gate, which makes your requests a reality and guaranteed with security using a virtual private gateway (VPG). Allow me to introduce it to you.
Background
Private IP addresses are rejected by the gateways of devices that communicate on SORACOM Air. In principle, direct connection between the Internet and devices is impossible because devices need to have public IP addresses to communicate via the Internet.
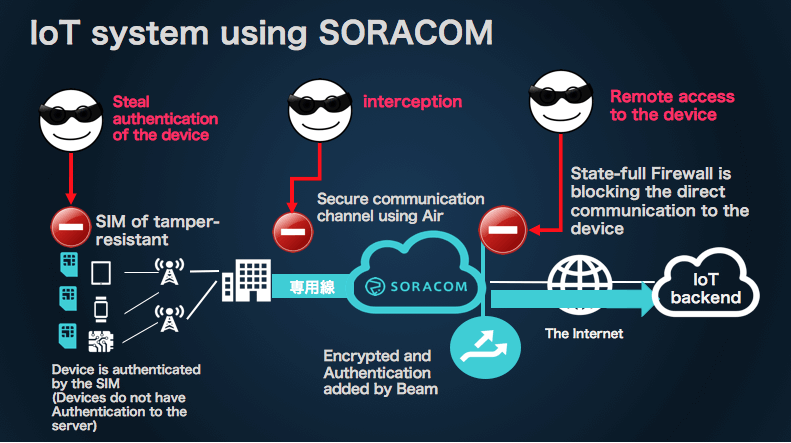
While you can easily access devices when communicating with a public IP address, there is the risk of opening up your IoT devices to attacks from the Internet, making it a security concern and therefore not a viable option. And so users have been searching for a means to access their devices as conveniently as possible while ensuring security.
Past Experiments
Previously, a number of attempts have been made to access devices communicating on SORACOM Air from the Internet.
- Using the M2M protocol MQTT by way of Beam
- Using SSH port-forwarding
- Using STUN/TURN for a general NAT traversal method
However, some use cases cannot be met by these methods — e.g. A professional-use IP camera that does not support STUN.
I use Raspberry Pi for a verification environment at home. Since I often have a need to login via ssh for configuration and programming changes, I connect it to a LAN for maintenance purposes instead of SORACOM Air. Since devices don’t always have easy access to LAN, performing maintenance over 3G/LTE surely makes most sense.
An Overview of Soracom Gate
The basic architecture can be seen in the following diagram.
※As with Canal and Direct/Door, it is essential that you use a VPG to use Gate.
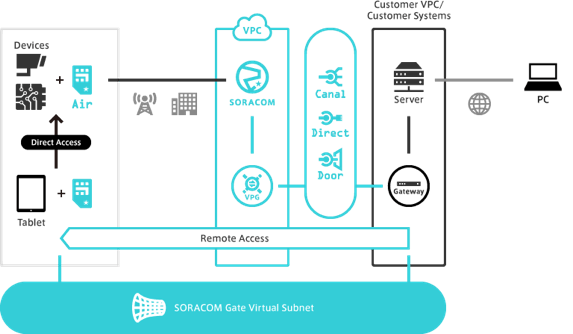
The virtual L2 network, also known as the “SORACOM Gate Virtual Subnet,” is displayed at the bottom.
First, open Gate for the VPG, that will virtually connect all devices connected to that VPG to the Virtual Subnet as well, enabling communication between devices.
Next, using Canal, Direct or Door, connect the VPG to a node (an AWS instance or on-premises server network device) with a VXLAN protocol. Having the node and devices participating on the Virtual Subnet virtually belonging to the same network via the VPG, users can now easily access services using a private IP or login via ssh to perform maintenance.
Animated Demonstration
The above configuration diagram depicts logging in to AWS instances via the PC and the VPG and using HTTP or ssh to access the Raspberry Pi address 10.193.19.136. Seen from the VPG instance perspective, it looks like the device is simply connected with the address as though it is in the same LAN.
Additional Information
SORACOM Gate is available today. Please refer to the following guide regarding usage.
- SORACOM Gate Usage and Device Access
Conclusion
The design for Gate’s icon is based on holes that open up in space when space-ships employ their warp drive in sci-fi films. I hope it evokes in you the feeling of being able to warp right from the server or terminal to your devices.
![]()
Matsui, SORACOM Team.