For Industry 4.0, OEMs Need a Cellular First IoT Strategy
On the journey to Industry 4.0, the first step is getting assets connected to the cloud. But what type of connection should you use? WiFi? LTE Cat-1? NB-IoT? The acronyms alone are enough to make anyone’s head spin. In this post, I’ll dive deeper into why OEMs should connect their equipment to cellular instead of other connectivity paradigms.
For long-range connectivity scenarios, like sending data from a remote device to an AWS server, the choice essentially boils down to WiFi or cellular. We normally think about this as the difference between “internet” service and “data” usage on a mobile phone. To generate WiFi service, an internet service provider lays cable underground and sets up local hot spots in a given neighborhood or area. For cellular data, a mobile network carrier constructs chains of cell towers, creating a mesh network that blankets a wide region.
If you’re an equipment manufacturer, you can already spot why an IoT architecture based on hot-spot connectivity could be problematic. Primarily, equipment is often remote and in hard-to-reach areas. Hygrometers might be in a remote desert; pulse radar level sensors for reservoirs are often located on top of hills or plateaus away from city centers; offshore oil wells with thousands of pieces of equipment may be more than a dozen miles from the coastline. The critical nature of these assets requires a reliable and secure connection.
The Reliability of Cellular
Both WiFi and cellular operate in the radio spectrum, and in most countries, the government or an associated body licenses a portion of that spectrum to mobile network carriers. The unlicensed portion is considered “public” and, as such, supports many different types of devices.
WiFi operates in the unlicensed spectrum, meaning any of the roughly 8 billion approved devices out there could interfere with critical connectivity, including:
- microwaves
- bluetooth-enabled devices
- fluorescent lighting
The problem is exacerbated by the actual implementation of a WiFi network, where even the most well-designed system has dead spots. Roaming from access point to access point, searching for consistent connection, is not a luxury most OEMs can afford.
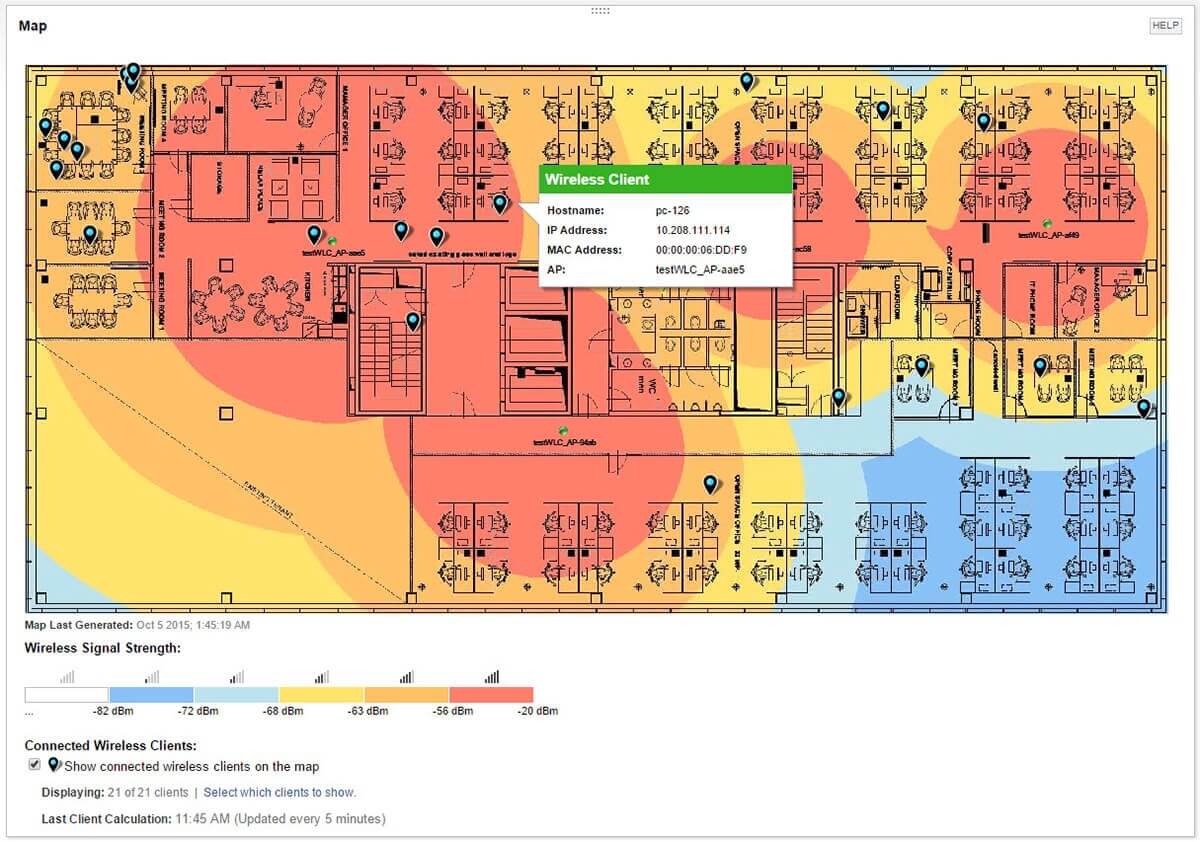
Adding an entire system of devices into an existing WiFi network also requires integrating with an IT department or system that can be:
- outdated (some operations still run on MS-DOS and require an IT specialist who understands legacy OS)
- restrictive (opening ports, resolving IP routes, NAT debugging)
- located on an entirely different continent
With a cellular connection, you’re assured a dedicated, licensed piece of the spectrum pie. Mobile network operators compete at auction, to the tune of 8 billion dollars, ensuring exclusive ownership of certain frequencies. And integration is instead handed over to a mobile virtual network operator, skipping the internal IT headache altogether.
Cellular Offers enhanced Security
Between cellular and WiFi, there is nothing from a pure technology standpoint that increases the attack surface either way. Modern WiFi connections, just like mobile carrier connections, utilize packet encryption that makes it difficult for malicious actors to steal data on the wire.
A key difference is that most attacks on a cellular network require the simulation of a cell tower. Successful attacks in the past have targeted the ‘um’ layer, the underlying SS7 protocol, or a blanket DDoS. These are often sophisticated attacks, leveraging one or more of the following:
- radio scanners
- cellular tower connection hub
- network admin access at a major mobile carrier or operator
- enormous compute power
Cracking a WiFi network? Type in ‘admin’/‘admin’, or whatever else the IT department decided to set and forget after the first week. Alternatively, use the publicly available ‘krack’ attack, which exploits WPA2: the default protocol protecting every modern WiFi network. Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and others have all released updates in response during the past year, but industrial routers lag behind their consumer counterparts.
An additional security benefit is working with a mobile virtual network operator (MNVO). Not only do you prevent vendor lock-in with a single mobile network carrier, but these companies do not own the actual infrastructure (cell towers) that the mobile network carriers built. Instead they lease the spectrum and provide services on top of them, giving you complete control over how data is handled. For instance, Soracom offers a wide array of security measures, from a private access point name (APN) service to private peering directly from your device to an AWS Virtual Private Cloud (VPC) via a cell tower. Your device data is never exposed to the open internet.
Connecting any device, let alone a critical industrial asset, carries an inherent risk. However, between WiFi and cellular, connecting via an MVNO can drastically reduce the attack surface.
“The three golden rules to ensure computer security are: do not own a computer; do not power it on; and do not use it.” — Robert Morris
Cost and Maintenance of Cellular Connectivity
While many IT departments already have WiFi implemented, OEMs that need reliable and secure connections will find it’s worth considering the extremely cost-effective cellular options available. A SIM card enabling connectivity can be purchased for as little as five dollars, with pay-as-you-go usage plans. Instead of buying 2GB of data a month, regardless of actual usage, an equipment manufacturer can pay for the 50 times that a sensor is triggered in a given day. In cases where usage is low, cost for data could be as low as $1/month for an entire network of devices.
There is also the issue of maintenance to consider. For assets in hard to reach locations, maintenance may only occur once a year, with each unplanned visit costing an enormous sum. Thus, it is critical that certain elements, like battery life, are extended in these environments for as long as possible.
To that end mobile network carriers recently started supporting LTE-M, or long term evolution, category M1. These devices can enter a deep sleep mode, only waking when a sensor is triggered. Estimates peg battery life at up to 10 years on a standard 5 volt battery. Given how low power, low bandwidth these devices are, the cost is correspondingly low as well. In fact AT&T recently published rates of $1.50/month/LTE-M device.
Cellular connectivity reduces maintenance in a cost-efficient way and in many cases will provide the reliability and security standards that WiFi struggles with.
…
At Xemelgo, we have worked with Industrial OEMs for many years, helping them build their IoT systems from the ground up. In our next post, we’ll cover some of the pitfalls we encountered from attempting to connect via WiFi. We’ll also dive deep into why we partnered with Soracom to connect our customers to AWS IoT through cellular.
We hope you’re enjoying the journey to Industry 4.0!